VINCERE TRUST
Always safe, secure and in the Cloud
Thousands of users trust Vincere every second, everyday to keep their data safe and carry out business-critical operations that help turn profits.
That’s why we’ve taken a no-nonsense philosophy when it comes to security, reliability and privacy of our Cloud-native applications.
Pentests, Vulnerability Scanning & Assessment
To provide independent assurance on our commitment to security, we engaged Bishop Fox - a third-party security specialist and certified Google Partner - to assess the security and vulnerabilities of our application and Cloud infrastructure across these four key areas.

Best-in-class datacenters
We use Amazon Web Services (AWS) which manages a comprehensive control environment that includes the necessary policies, processes and control activities for the delivery of each of the web service offerings in a secure manner, so you can be assured that all your data is safe in the Cloud.
Data center locations
Our deployments are hosted in 5 locations. We use top tier AWS data centers, strategically located close to you to ensure the highest performance.

Data & network security
Protection of data from unauthorised parties both from within the organisation and externally:
Data integrity
In order to protect and maintain the accuracy of your data against malicious threats and attacks, we adhere strictly to the Data Leak Prevention (DLP) procedure.
• Encrypted over HTTPS (SHA2 encryption) – a protocol that provides secure communications through the internet. Rest assured that your activities are as secure as internet banking.
• Data at rest + Data at transit protection via encryption and cleansing.
• Systematically, we create logs on all output channels for periodical checks.

Compliance
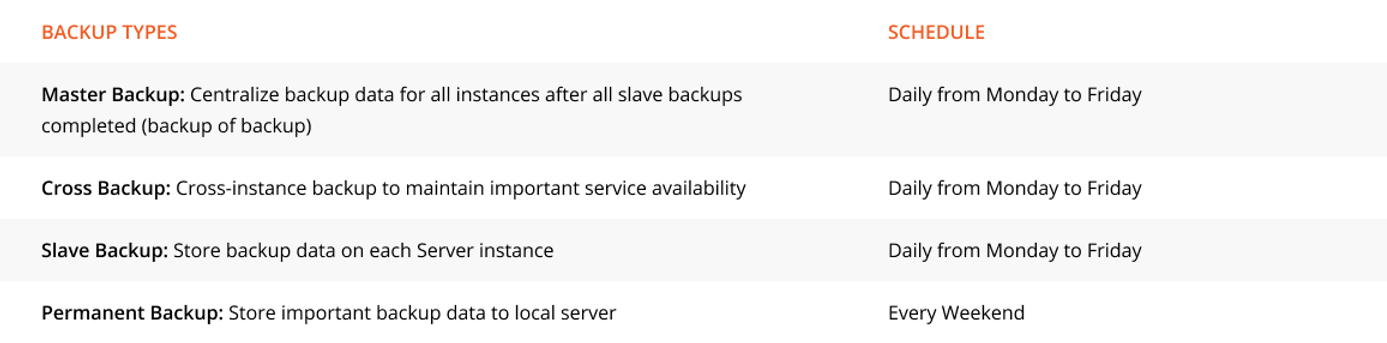
Backup schedules
We have strict backup procedures and have put in place recovery plans to ensure quick restoration with minimal loss of data. When it comes to disaster recovery and your data, our mission is to keep the Vincere Cloud & services running at all times with the least disruption – and that’s our promise to you.